As SAML 2.0 depends on trust, it is necessary to establish this trust by exchanging the metadata of the IdP and SP. When the SAML 2.0 client for Gateway (NPL001) was created, the metadata of the Gateway SP was important to Keycloak. In this step, the metadata of the IdP is exported from Keycloak to be able to import it to Gateway. This concludes the task of establishing a trust between SAP Gateway and Keycloak.
Download Keycloak IdP Metadata
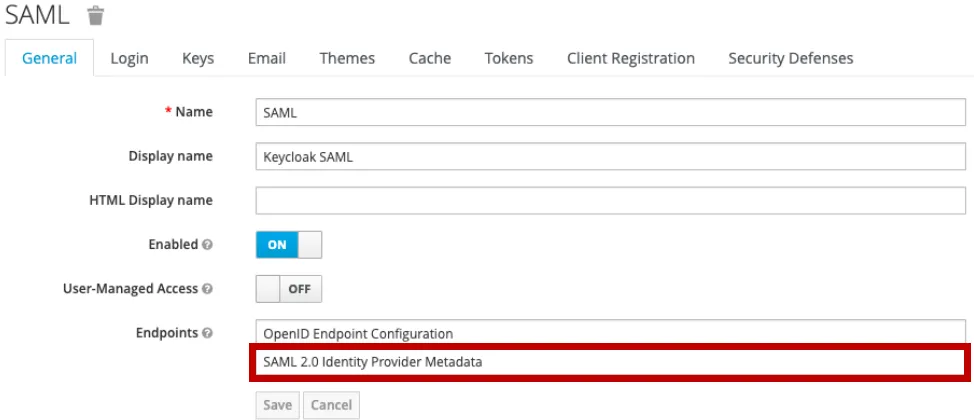
Log on to Keycloak, select the realm and go to Realm Settings.

The SAML 2.0 IdP metadata download link can be found at Endpoints. Click on SAML 2.0 Identity Provider Metadata.
Alternatively, the IdP metadata can be downloaded directly from the descriptor URL.
<keylcoak server>/auth/realms/<REALM>/protocol/saml/descriptor
In my case, the URL to download the metadata is:
http://localhost:8080/auth/realms/SAML/protocol/saml/descriptor 🔗
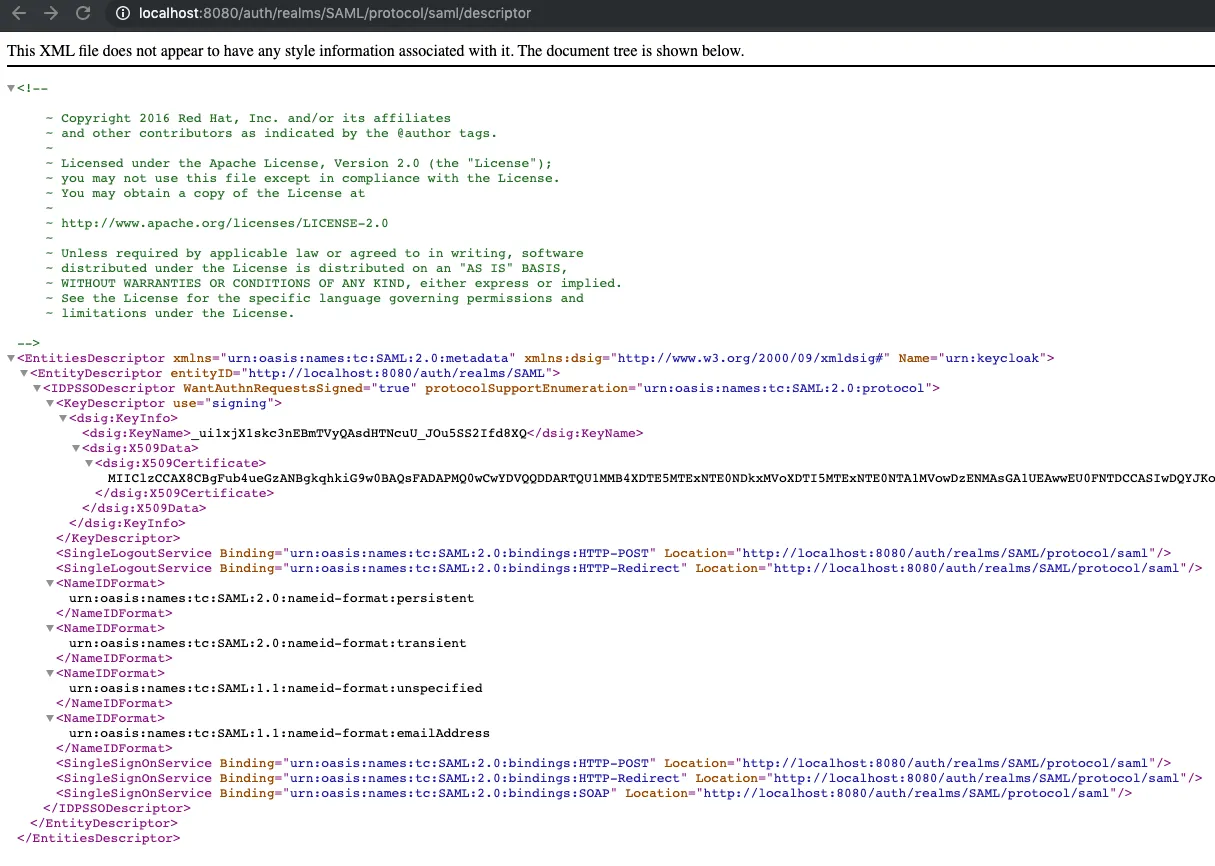
Here you can see a sample metadata file. It is also available 🔗 on my repo on GitLab.
<?xml version="1.0" encoding="UTF-8"?>
<!--
~ Copyright 2016 Red Hat, Inc. and/or its affiliates
~ and other contributors as indicated by the @author tags.
~
~ Licensed under the Apache License, Version 2.0 (the "License");
~ you may not use this file except in compliance with the License.
~ You may obtain a copy of the License at
~
~ http://www.apache.org/licenses/LICENSE-2.0
~
~ Unless required by applicable law or agreed to in writing, software
~ distributed under the License is distributed on an "AS IS" BASIS,
~ WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
~ See the License for the specific language governing permissions and
~ limitations under the License.
-->
<EntitiesDescriptor Name="urn:keycloak" xmlns="urn:oasis:names:tc:SAML:2.0:metadata"
xmlns:dsig="http://www.w3.org/2000/09/xmldsig#">
<EntityDescriptor entityID="http://localhost:8080/auth/realms/SAML">
<IDPSSODescriptor WantAuthnRequestsSigned="true"
protocolSupportEnumeration="urn:oasis:names:tc:SAML:2.0:protocol">
<KeyDescriptor use="signing">
<dsig:KeyInfo>
<dsig:KeyName>_ui1xjX1skc3nEBmTVyQAsdHTNcuU_JOu5SS2Ifd8XQ</dsig:KeyName>
<dsig:X509Data>
<dsig:X509Certificate>MIIClzCCAX8CBgFub4ueGzANBgkqhkiG9w0BAQsFADAPMQ0wCwYDVQQDDARTQU1MMB4XDTE5MTExNTE0NDkxMVoXDTI5MTExNTE0NTA1MVowDzENMAsGA1UEAwwEU0FNTDCCASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoCggEBAOYhrefNGcAqMFDEG06GxSpc/cwRUkKrN/D4/i83w6AlWz0hBqBLoGCHP30b5jX9674B7b9OaP/9dLi7p+V61Mb7lDRrIAtXo7FHRflcMVBWTBF6X3ztYliIY2liDv2GAZudbGTwTNdq+gZmdFyoJ/gvDaCW527ltbRSYhGXFZgBPNqrFxiP4FMKGtQ8tbzv0Rxt4Ez7pqAK+Kh7f3zKGwk/7fvENKrrfzHY4XoHmNBpErUeoaE6wcW5EX/fJe37VS7AyKd6jHaDa3nvvrFREUOBceqtmIIHnv/SZExzIXz/jQWQx9lGaqiuUCQ4G4dtGSTCo+izqRvOxm1pcwMh+T8CAwEAATANBgkqhkiG9w0BAQsFAAOCAQEAyGnbodezduakIMI/SoxUX8W4PnIzPrBcirMYAnZOKql/Mp8pyDdWNun3Fjsd8A7X9R83mx3msgXGN0RPbgI5dEgWWWLZ4x+yYWURMk3W1zE/UaTRjf/hXNW5vbS4RE/MaPTHOaFRZjXoS2t3FNS4hRvncMrTL5JAWBabhqY+zwai/qXDaG9IyZIirJJp+PwX+u58phR1tbPSG+tHUIPJPICEyoczViVMbIJAJ0M5jTy2/W3+CPkO1BxCOeXvZAmeK9lwn3qbL+nHbiHYgUULAw4lcysDgT0ogZKj12cCxH4UsMo1hSb8ATy+5mjYUlKSzQTNBGcbY/glKM1SQa3YyA==</dsig:X509Certificate>
</dsig:X509Data>
</dsig:KeyInfo>
</KeyDescriptor>
<SingleLogoutService
Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST"
Location="http://localhost:8080/auth/realms/SAML/protocol/saml" />
<SingleLogoutService
Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-Redirect"
Location="http://localhost:8080/auth/realms/SAML/protocol/saml" />
<NameIDFormat>urn:oasis:names:tc:SAML:2.0:nameid-format:persistent</NameIDFormat>
<NameIDFormat>urn:oasis:names:tc:SAML:2.0:nameid-format:transient</NameIDFormat>
<NameIDFormat>urn:oasis:names:tc:SAML:1.1:nameid-format:unspecified</NameIDFormat>
<NameIDFormat>urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress</NameIDFormat>
<SingleSignOnService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST"
Location="http://localhost:8080/auth/realms/SAML/protocol/saml" />
<SingleSignOnService
Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-Redirect"
Location="http://localhost:8080/auth/realms/SAML/protocol/saml" />
<SingleSignOnService
Binding="urn:oasis:names:tc:SAML:2.0:bindings:SOAP"
Location="http://localhost:8080/auth/realms/SAML/protocol/saml" />
</IDPSSODescriptor>
</EntityDescriptor>
</EntitiesDescriptor>