SAP Cloud Availability Service
The access to the app is not any longer allowing external users (like S-User) to log on. While the public page of the app is accessible, you cannot read any evauations or other data. SAP acted here very quick and tightened the SSO access in just a few hours.
The SAP Cloud did not have the best week recently (11. September 2023). Some services were not available for a few hours. Nothing new, nothing to worry about too much.* Services returned to normal state after a while and in case you were affected, you check the status page. The page SAP provides is for creating trust – guess why the page is located under trust center. Just that the communicated status was not exactly what you might expect. This started a small discussion on Twitter. The discussion was joined by Lars, Nabi and Marc sharing their experience and escalated rather quickly when Nabi posted this tweet:
The post contained a link to an app that I did not know existed: SAP Cloud Availability App.
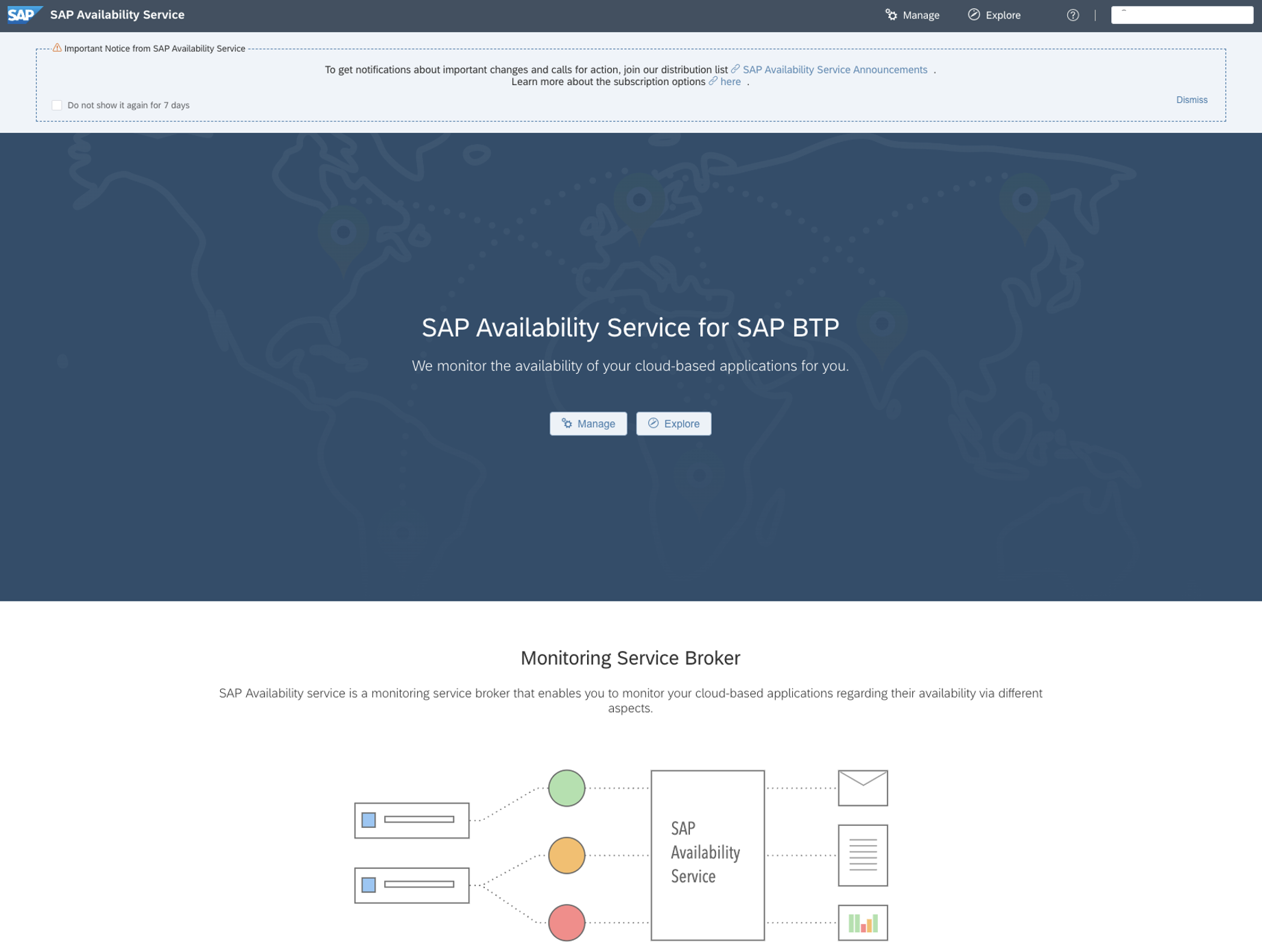
The App
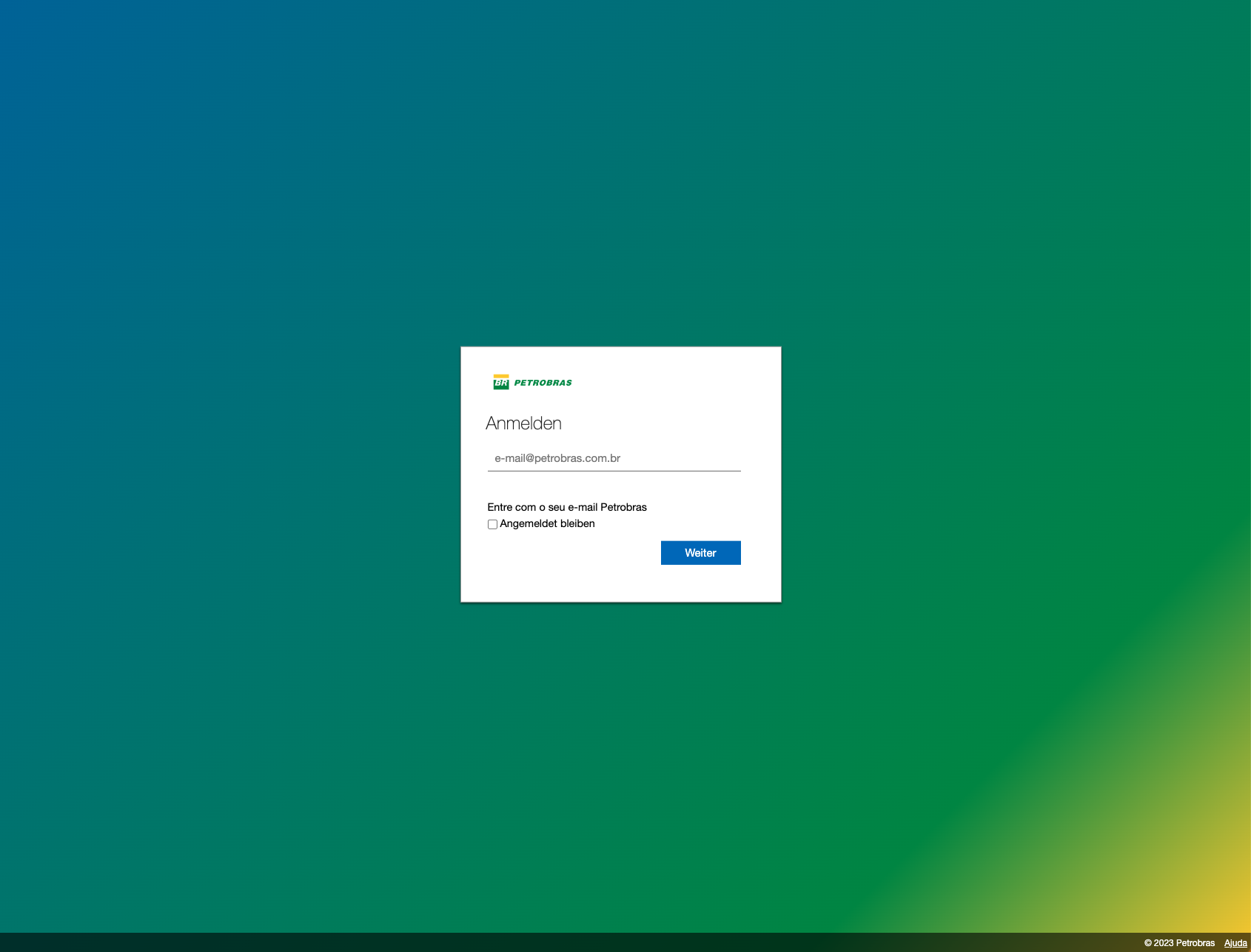
The app is protected by logon, and I needed to use my S-User. I did not try this out with my private P-User, because, well SAP Universal ID. My S-User worked. So far, so good and access to the app worked. If I get access to an app, I assume that I am allowed to use the app. Specifically when I first have to log on, as than also role management is in place.
Unfortunately, the app it is not an UI5 app. Not sure what the app does, but it is rather easy to navigate. The explore button gives an interesting access to information provided by the app.
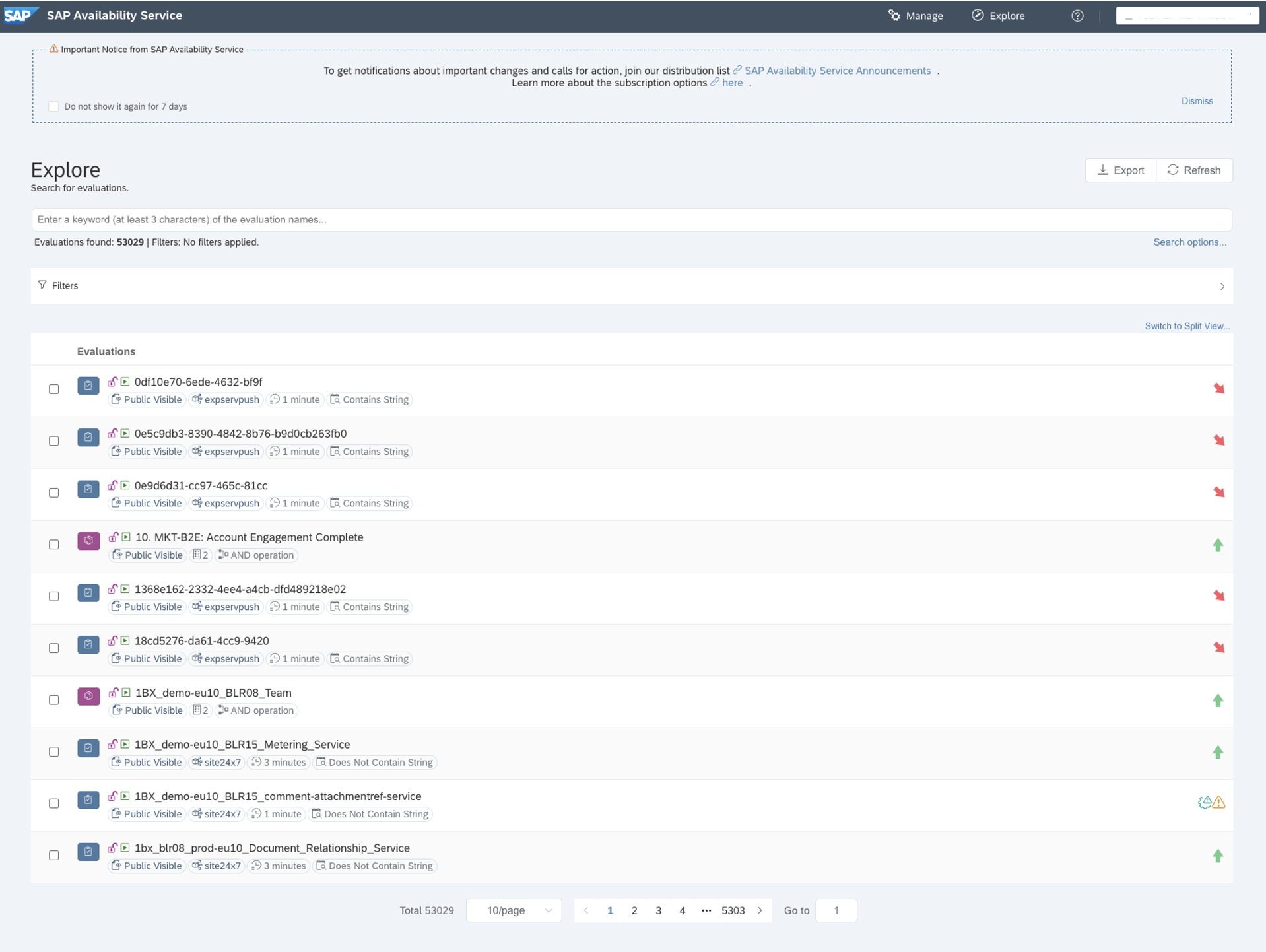
Monitoring information
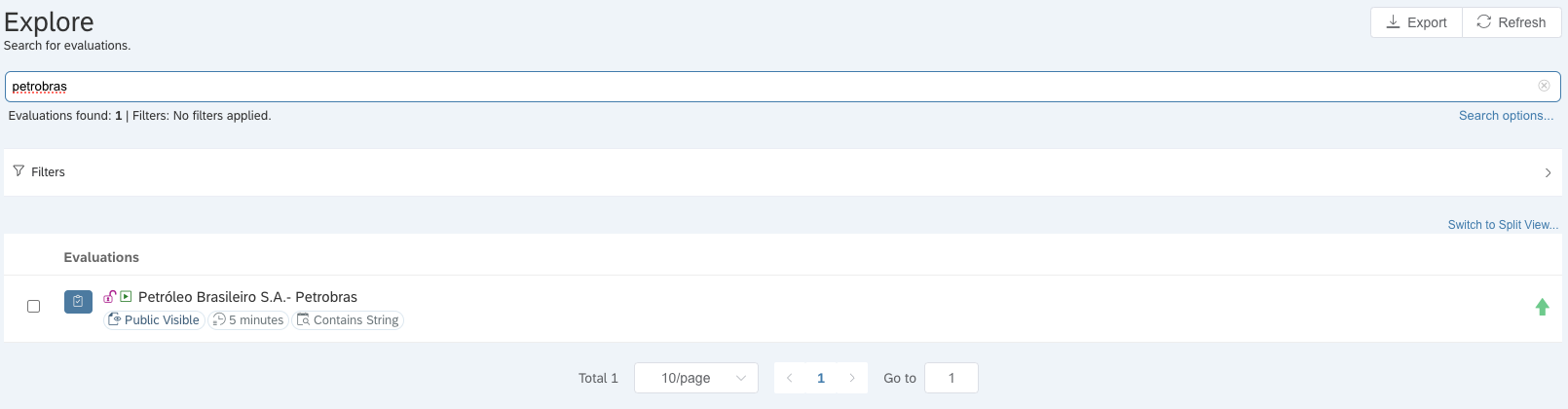
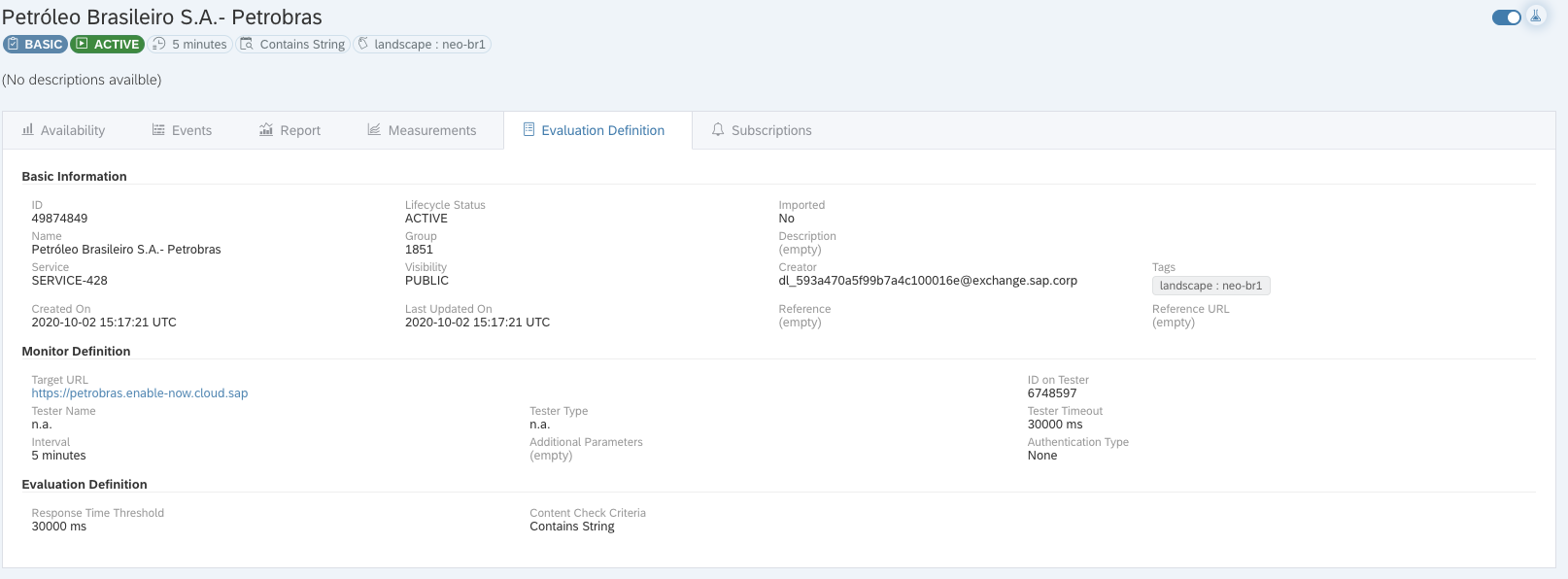
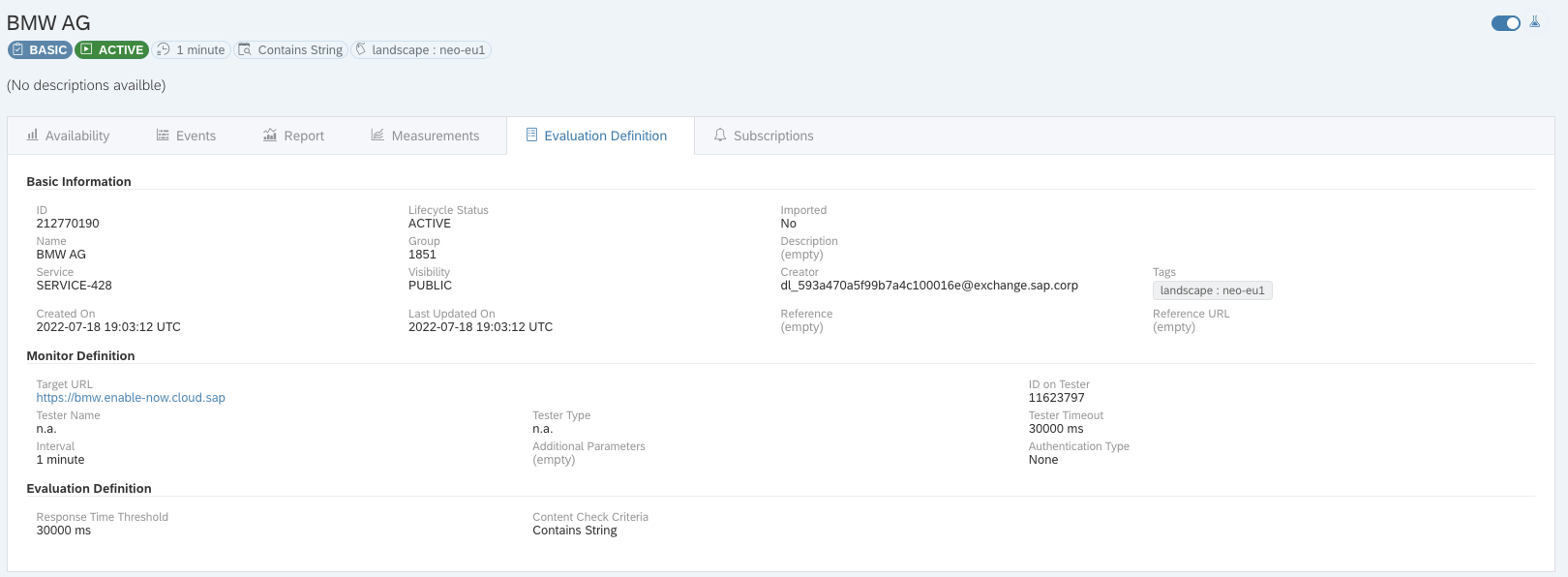
The app allows to access monitoring information. They are called evaluations. These are created for specific BTP services. It gets interesting as these monitoring services contain customer names. Here in the example the configured monitoring with the name Petrobras Brasileiro S.A. While the name could be freely chosen, I know that this is an SAP customer. That I can see this with my S-User from a different company, not related to the other company, is unfortunate. The reason is that the visibility of the evaluation is set to public. And not e.g. to SAP internal. As long as SSO works, and the app accepts my S-User as a valid user, I can log on and see the public visible monitoring data.
I can access the details of the monitoring and even see if a service is down or not.
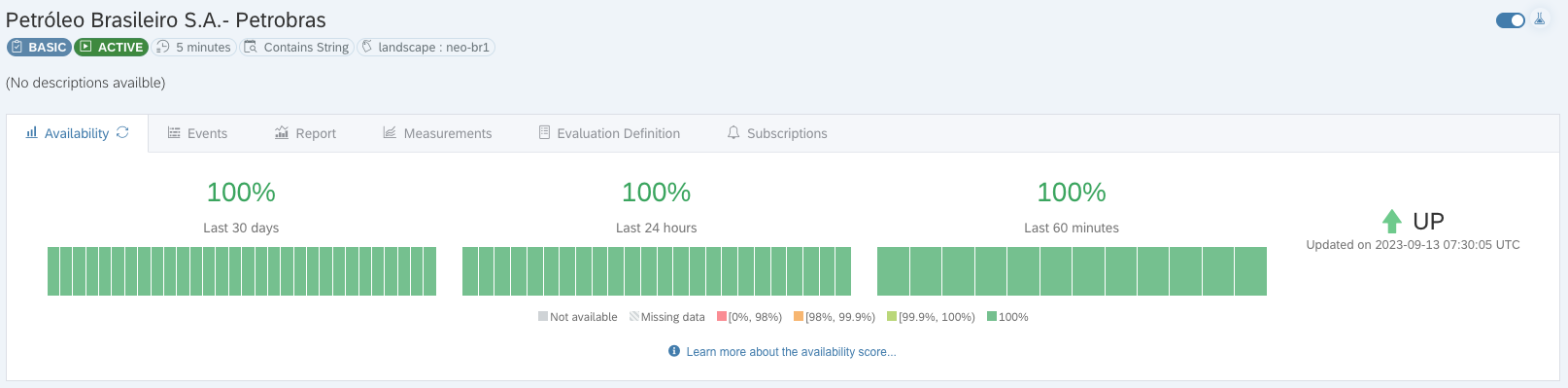
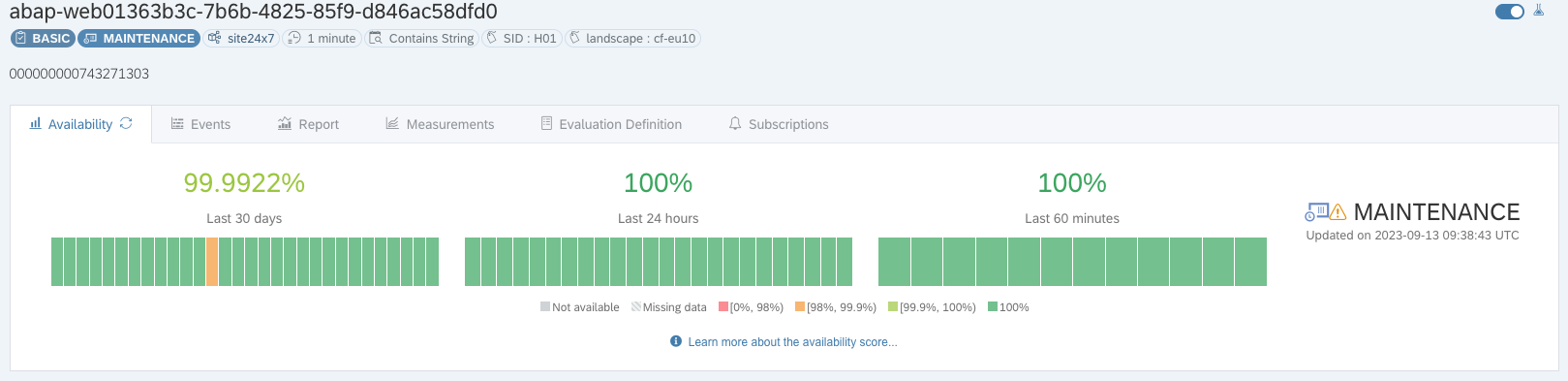
Another service with some smaller problems. Just to show that the app works nicely and records availability issues.
In the details I can explore more information for the given customer. It is not much, but the link to the enable now page is available.
To access, you need to have a valid user.
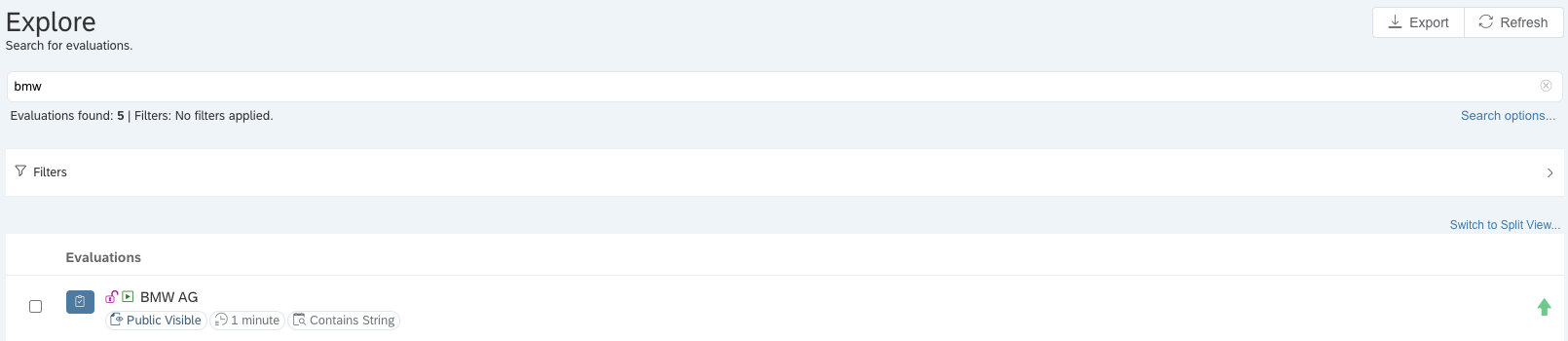
Of course, this works also for other companies. Example: BMW.
Filter data
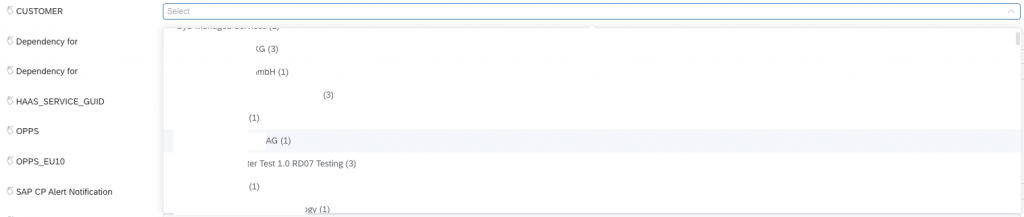
So far, the Cloud Availability app is “only” providing some interesting data that might be useful for a social engineering attack. If you ask: only? Yes, we have seen worse from SAP. But the post is not finished here, I promise will get there. The app shows configured monitoring setups for different SAP Cloud services. But there is more to it. You can filter the evaluations. The app provides filter values. Many filter values. And they work. So yes: jackpot. The app provides a rather huge list of information that you would not expect to be accessible so easily: customer names, account IDs, organizations, etc.
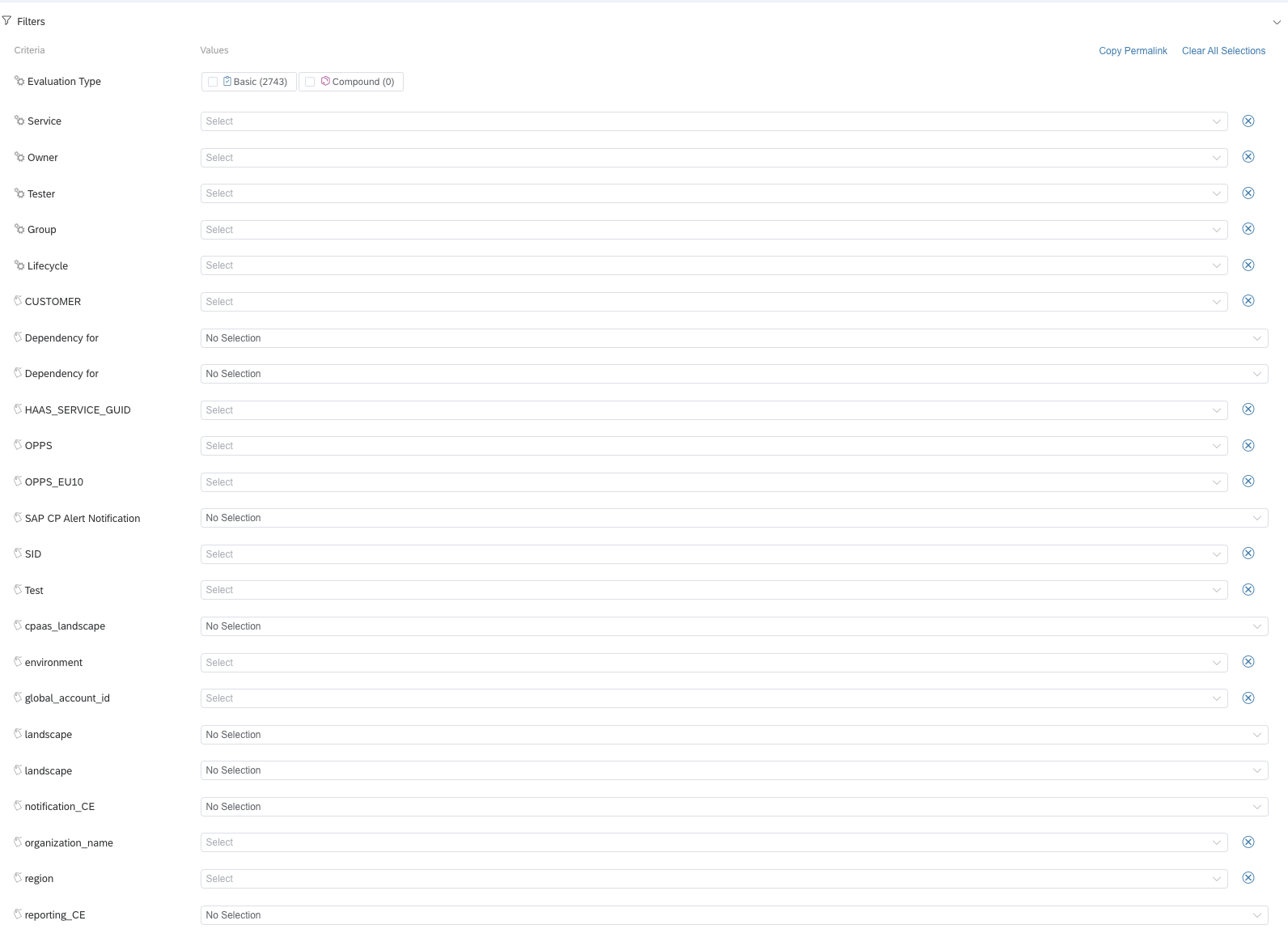
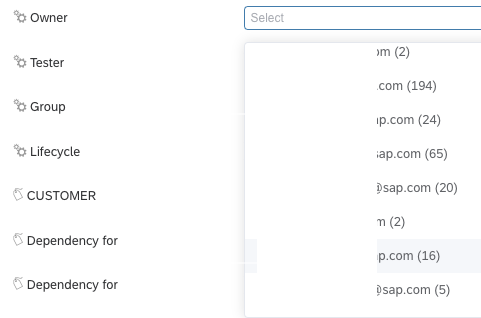
You get a list of SAP employees.
A list of customers.
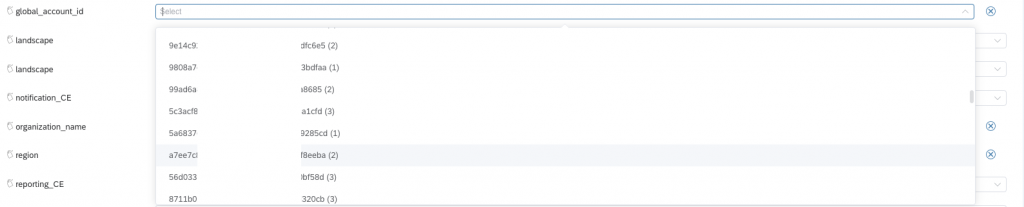
Global Account IDs
Subaccount IDs
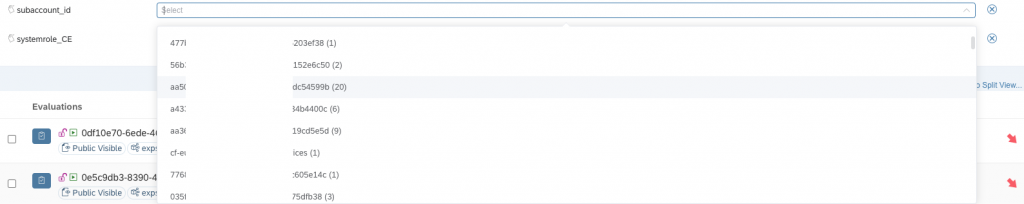
Not sure if the global and subaccount IDs are real customer IDs. Maybe you might want to check out if your ID is in the list.
API access
Going through the value helps is not the best approach to get access to data. The app loads data at startup, and that information can be loaded manually too. To get a list of possible filter values:
https://availability.cfapps.eu10.hana.ondemand.com/api/ui/evaluationmetadata/overview
The JSON response contains several useful information like the e-mail addresses of the owners (owners: SAP employees).
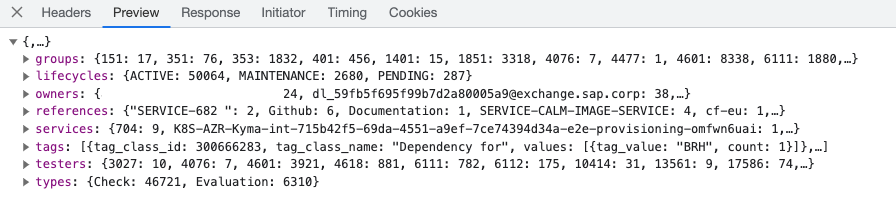
Information about customers, organization, account id, etc:
https://availability.cfapps.eu10.hana.ondemand.com/api/v1/tagclasses
There are several blocks in the response that might be interesting: space names, organization names, account ids.
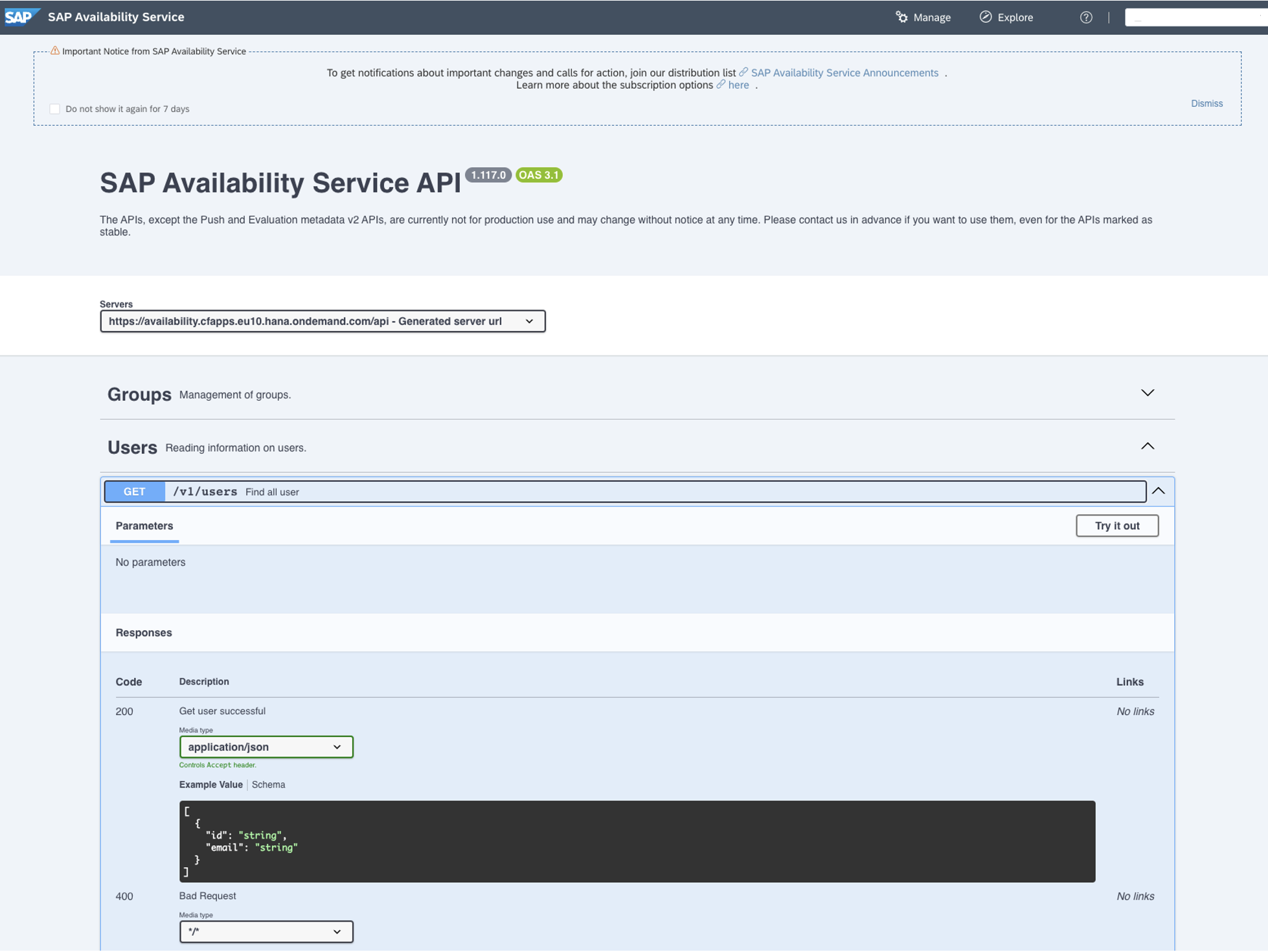
Fortunately, you do not even have to user the developer tools of your browser. The app provides an API and a nice documentation. For instance, for the User API:
Status so far: as usual. FUBAR
What can you use the information provided by the app for? Sure, social engineering. You can see some SAP customer information. Get some idea what they are using from SAP Cloud: CF, Neo, services. But most is very technical and used for a rather low-level monitoring. Of course, every piece of information so far should be better protected than just with SSO and then give all users access to sensitive customer information. Or SAP employee information. So far, the app is the usual problem when “At SAP security is priority #1” meets reality. Internet is not intranet. A not public URL is not secure. If it is made public, people can access it. The URL is on Twitter, it is published in this post. The URL is public. The visibility for the information – evaluations, filter values, etc. – cannot be set to public or all authenticated users. Customer data is leaked. Not only the name, but also services they are using from SAP. SAP Cloud, region, services, some monitoring data. An attacker might use this to get in contact with an administrator after an issue shows up. How find out in a timely manner that there is an issue? You can subscribe to evaluations. Did not try this out, but if it works: maybe not so good.
The app seems to be targeted to an internal audience. The help link points to an internal server, *.wdf.sap.corp. I’d like to say that this is a clear indication that the app is for internal audience, but hey, it is SAP. They posted so many times internal links to external audience … I guess the fact that a normal S-User can access the app and see data is as intended. Just that the security part here is to not publish the URL I wonder if there is any default SAP BTP security access mechanism available that makes apps only available if you connect via VPN, or from a specific location. Currently, apps published in BTP are publicly available, you just need to know the URL.
Securing the internals of the app is work, and SAP should start to not see this as costs. If it takes weeks or months to secure an app by design, than just do it. The app seems to offer value. But access must be restricted. Visibility of evaluations cannot be set to public. Filter values visibility must be restricted.
* Yes, 100% resignation. We have been there 5+ years ago, and uptime, monitoring, transparency is still not perfect. After all these years, why fight for this? The current level seems to be the best SAP can deliver, so be it. I mean, just think about the security dashboard.
1 Comment
Andy · September 21, 2023 at 22:56
Gott Sei Dank dann eben doch nur am Rande des Wahnsinns